OWASP crAPI: Introducing API Security the Hacker Way


How well do your teams understand your APIs?
Vague answers? So is the understanding in many cases. Understanding APIs and their attack vectors are complicated. On top of it, there’s no standard way to provide that hands-on experience of an enterprise API design fallacies and mistakes that lead to vulnerabilities. And many security engineers, developers, and researchers very well agree with this.
There are assumptions made in the development life cycles of API-centric applications, and many times shortcuts are taken to provide more features in a short amount of time. Such assumptions could be:
- All my internal APIs are secure since they do not interact directly with external users but are meant to be used by other external-facing services.
- I do not need to handle role-based access controls (RBACs). Instead, the identity team should implement it in the API gateway.
The disconnects, the shortcomings, and the misunderstandings all together lead to the creation of zero-day vulnerabilities that can significantly impact revenues and tarnish the brand image.
“Shift left is not just about shifting your tools and process but the knowledge as well.”
Taking the first step, we built a vulnerable application that is purely API-driven, simulating a microservice-based enterprise architecture through which we can “shift left” the knowledge and experience we have gained along our journey. And this is how crAPI (“Completely Ridiculous API”) was born.
So, what is crAPI?
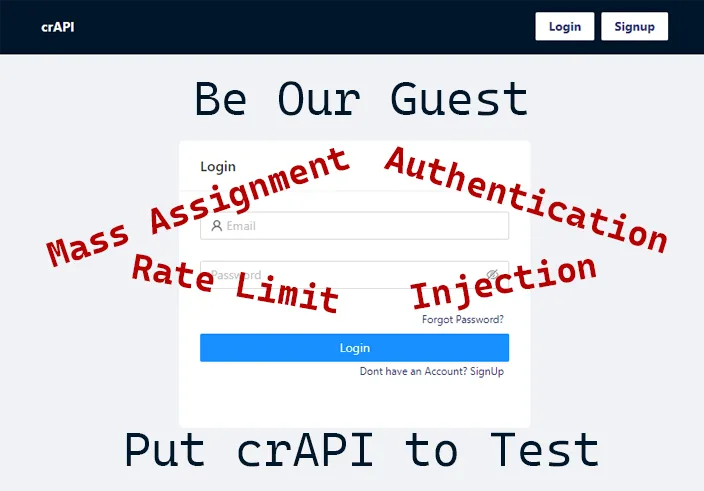
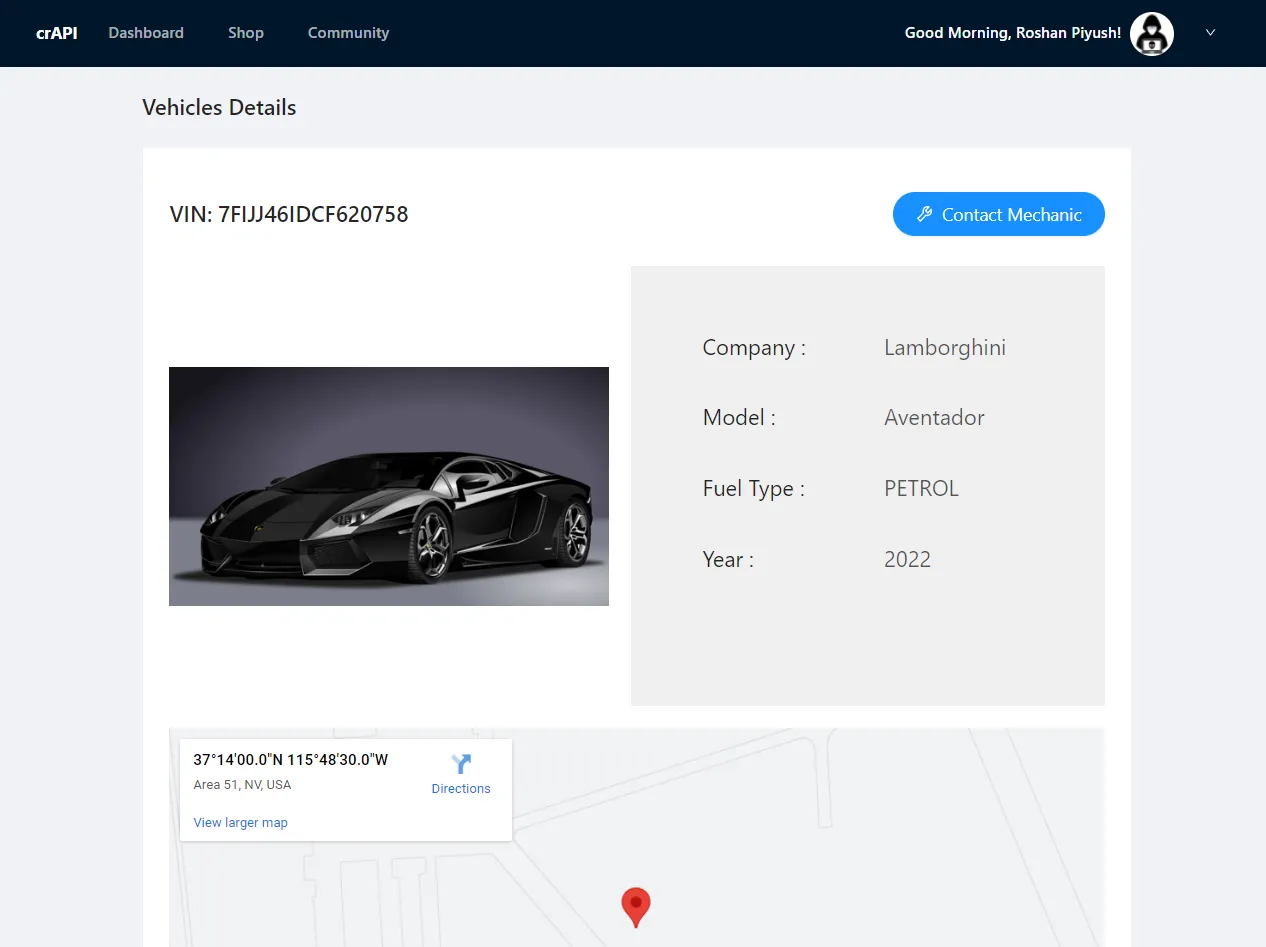
crAPI is a platform for vehicle owners to register and manage their vehicles. Following in the footsteps of Webgoat and JuiceShop, crAPI is an intentionally vulnerable application. However, crAPI is primarily filled with API vulnerabilities for teaching, learning, and practicing API security.
Open Source and Community-driven!
Gone are the days when tools were like a secret sauce. We built crAPI, keeping security engineers and developers in mind, and open-sourced it so everyone can contribute learnings and experiences they had during their security battles.
What does crAPI provide? (Is it yet another vulnerability simulation tool? No!)
An authentic experience of how a single vulnerability or a chain of vulnerabilities can escalate quickly to put your applications/services under threat.
- crAPI specializes in the common vulnerabilities in modern API-based applications, including those in the OWASP Top 10 for APIs.
- All the challenges in crAPI are based on real-life vulnerabilities found in APIs of big companies like Facebook, Uber, and Shopify.
- crAPI exposes many different vulnerabilities, some of them are easy to find, and others require multiple steps and some creativity to exploit. As of now, you will not find the mundane XSS and SQLi challenges in crAPI.
How does crAPI help?
- Developers/Security champions can understand the causes of API vulnerabilities and practice their skills to fix them.
- Security enthusiasts get a practice playground for API attacks and hands-on experience in real-world enterprise applications.
- API protection tools can assess their quality to demonstrate detection and protection of API attacks.
Traceable’s support for the crAPI project
Traceable has open-sourced crAPI for the benefit of the broader security community, and we are committed to supporting the project and working with the community closely!
Building together
We will keep adding new vulnerabilities and challenges from all realms that affect API-driven development, making crAPI more ridiculous. In the meantime, we would love to hear your ideas, feedback, and suggestions. You can get started easily by following the guide here. If you face any issues, we are available on the #crapi channel in OWASP slack and always looking for awesome community contributors like you!
Roshan Piyush is Security Research Engineer at Traceable AI, which is solving API security using the powers of machine learning and distributed tracing. He has 8+ years of research experience mainly focusing on API security for the last 5+ years. He loves building security stacks, tools, and solutions. He is also a core member of the Owasp Coraza WAF team and a leader of the OWASP crAPI project.
The Inside Trace
Subscribe for expert insights on application security.
.avif)


.webp)
