Drop-in API security for your Kuma deployments
Kuma is a service mesh that makes the underlying network safe, reliable, and observable without having to change any code. Kuma is built on top of Envoy, enabling customers to deploy a ready-made solution that enables seamless management of any service on a network, including application traffic, as well as microservices and APIs.
However, service meshes do not provide the internal visibility and application context needed to detect and prevent impending cyber-attacks.
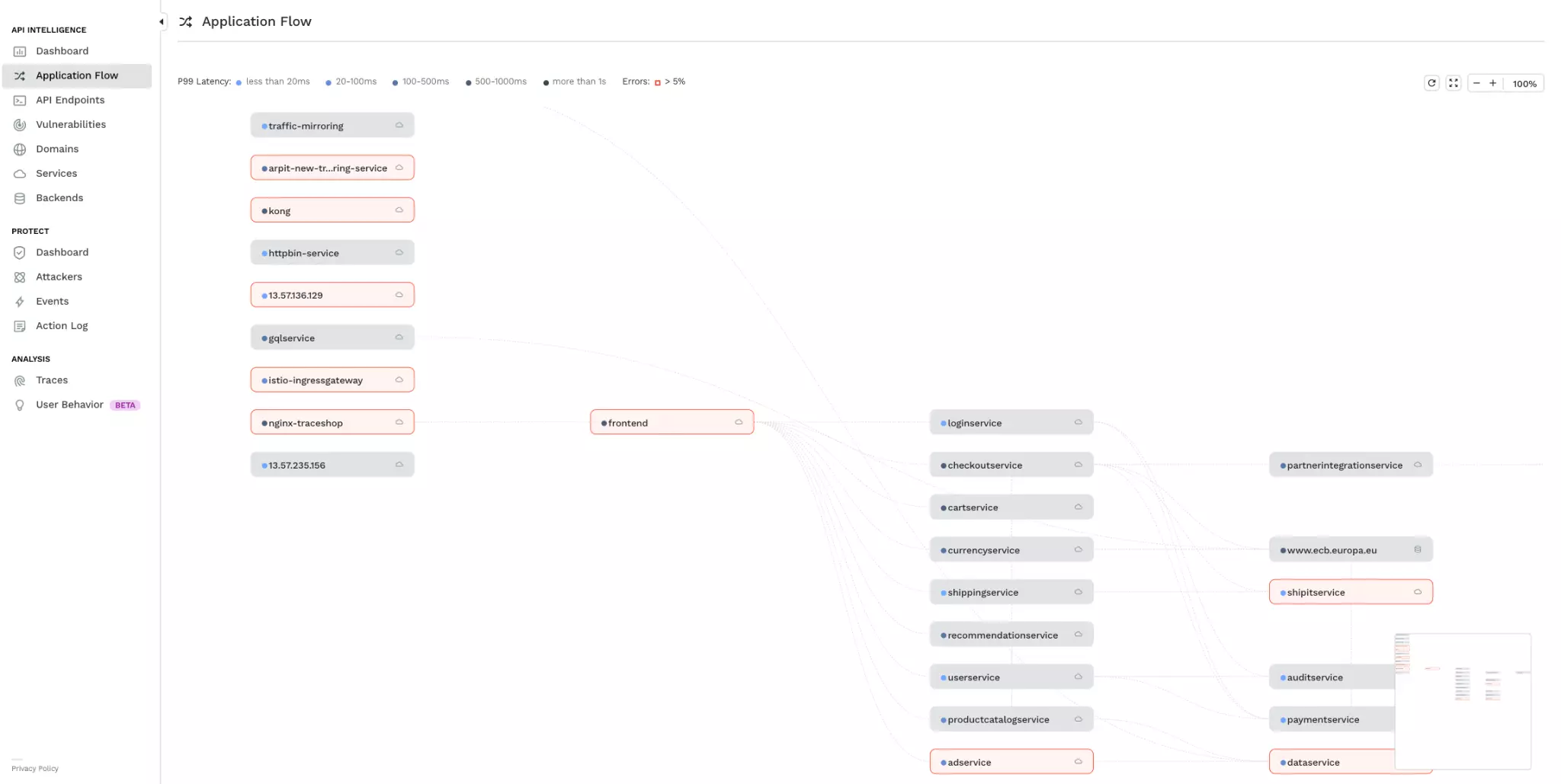
Traceable AI is able to provide for Kuma deployments an integrated API and application security solution that is able to learn the protected application in real-time. Powered by machine learning and distributed tracing, Traceable AI is able to deeply understand applications built on microservices architectures, enabling end-to-end security from user to data. Traceable AI can understand the inner workings of the application, how it changes, and normal baseline behavior that allows it to surface anomalies that can be alerted on or immediately blocked – ensuring your application is secure and resilient.
Read documentation for Traceable AI Kuma agent
Learn how
Traceable AI works
Key Benefits
API Discovery
API Intelligence & Risk Monitoring
Per endpoint risk scores and threat indexes help prioritize focus. Risk scores are continuously calculated based on the likelihood and possible impact of an attack. Threat indexes show the current level of threat activity.
Prevent Sensitive Data Exposure
OWASP API TOP 10 - API Protection
OWASP TOP 10 - Web Protection
Security Analytics
Resolve Threats Faster
Visualize security events as kill chains as executed by cybercriminals, helping to streamline threat analysis, forensics, and remediation.
Triage Attacks Faster
Decrease analysis time by reviewing aggregated security events without having to parse through hundreds of log files across microservices.